|
|
 |
|


Be on the wave or under it™
The News – 05/13/02
|
In this Issue:
|
Recommended Reading
|
|
|
I realize this is the only
newsletter you’ll ever need, but if you want more in-depth
detail, check out:
Stan Hustad’s The Coaching Connection
|
Bits & Pieces III
(The Broadband Content Wars series will continue
in a future SNS)
I really will get to the third part of the Broadband Content
Wars series, but so many important news nuggets cropped up this
week, I just have to share them all first.
- Congress May Delay Spectrum Auction: Congress
may delay indefinitely the FCC’s June 19 spectrum auction of
airwaves currently used by television broadcasters. The commission
has already delayed the auction five times but recently denied
a request by the Cellular Telecommunications & Internet
Association (CTIA) for an additional delay. The FCC is under
a legal mandate to sell airwaves used by channels 60-69 by Sept.
30.
AtNewYork.com
- Jargon Alert: CamelCase Prospective
SNS Reader Bill McTeer told me about a nifty new bit of jargon
recently. CamelCase describes the practice of joining words
by capitalizing the first letter of each word. It particularly
describes the common object-oriented method of naming variable
with a small first letter and internal capitalization, with
the resulting name looking like a bumpy camel’s back. The procedure
is also known as StudlyCaps, InternalCapitalization, and CamelHumpedWord.
Now if I could just understand what Bill told me about Microsoft
and TitleCase!
- Symbol Gets Mobile Enterprise Telephony Patent:
Voice-over-Internet Protocol (VoIP) is in relatively common
use in larger enterprises today. The technology digitizes voice
communications and sends them via IP packets over a wireline
network. Hardware maker Symbol claims to be the first company
to make VoIP commercially viable for devices over 802.11 wireless
LANs, and now has a patent to prove it. Symbol currently uses
the technology in the Symbol NetVision family of wireless voice
and data appliances. This patent has got to make the wireless
cell phone network providers a bit nervous. Perhaps this is
why Verizon and others have shown quite an interest in procuring
802.11 networks to complement their 3G efforts.
Symbol
-
Security
First Step: If you think the first step
your company needs to take in order to be secure is to buy
a firewall or other security hardware/software, think again.
Gartner asserts that the real first step for small and mid-size
businesses is to develop a comprehensive security policy.
They go so far as to recommend that no security decisions
be made until a policy is in place, which they say can take
three months to a year. Well, no matter how important the
security policy is, I think you still should get a firewall
as soon as possible.
TechRepublic
-
Tele-immersion
and Business Communications: Alert SNS
Reader Dean Cowdery sent along a link to a video presentation
of Jaron Lanier’s speech at the Tenth Annual Enterprise Value Retreat &
Awards Ceremonysponsored by CIO magazine. Lanier is the
guy who coined the term virtual reality and did a lot of pioneering
work in that field. He’s been working on the concept of tele-immersion,
the ability to be totally immersed in a virtual world where
you can collaborate effectively with coworkers at a distance.
Among the interesting infonuggets from his speech: People
need visual feedback within 30 to 50 milliseconds in order
to not experience discomfort due to lag (I’ve seen other estimates;
see a previous SNS); fiber optic
transmissions move at only about two-thirds light speed; the
best network performance, coast-to-coast involves about 30
to 50 milliseconds of lag. Lanier made a major prediction,
that tele-immersion technology will affect the size of corporate
work groups, which will tend to number about four people due
to the optimum configuration of tele-immersion displays. The
video is well worth watching.
CIO.com
-
Fear
the Shredder: Alert SNS Reader Dean Cowdery
also sent along a link that eventually deposited me at The
Shredder, a site that downloads the graphics and text at an
URL you feed it, shreds it and displays the chopped up results.
The image to the right is  what happened to the main
StratVantage page  after the Shredder had
its way with it. More graphics-heavy sites give better results,
like the picture to the left. It’s not useful, but it is interesting.
The Shredder
-
Cutting
the Cord: Forrester analyst Charles Golvin
predicts that 20 million telephone lines, 15 percent of US
lines, will disappear by 2006 due to the increasing trend
of people abandoning the home line and relying solely on their
cell phones.
USA
Weekend
-
Former Software CEO to Join KISS on Farewell
Tour: Cool headline, huh? The story it
tops relates how Steve Ballmer has tired of his duties at
Microsoft and will travel as a member of the “Why Are They
Still Here” ‘80s band KISS. It’s just one of the satirical
news stories available at Valley Of the Geeks, which was brought
to my attention by Alert SNS Reader Larry Kuhn. My personal
favorite is an acronym-laden
faux press release declaring middleware software maker BEA
as a leader in the TLA (Three Letter Acronym) market. BTW,
I recently heard longer-than-three-letter acronyms described
as ETLAs (Extended Three Letter Acronyms).
Valley
of the Geeks
-
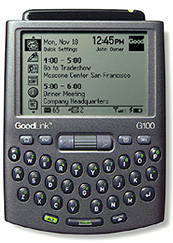 Good is Good Enough Good is Good Enough:
Alert SNS Reader Andrew Hargreave sends along a link to an
interesting handheld wireless device by a company with an
unassuming name: Good Technology. The Good™ G100 wireless
handheld is a compact and feature-rich handheld wireless device.
(And how the heck did they trademark Good™?)
The device works with the GoodLink™ wireless corporate messaging
system, has a 212 x 138 pixel 16-level grayscale screen that
can display up to 12 lines of text, weighs only 4.7 oz. (130g),
runs on an ARM-based processor, and sports 8MB Flash memory
and 8MB RAM. However, I feel that any new wireless device
on the market today needs to include cell phone integration
to have even a small chance of stealing market share from
the device giants. So good luck to Good.
Good
Technology
-
The
Out of Work Comics: Alert SNS Reader
Roger Hamm sends along a link to a real tale of woe. Odd Todd
is out of work, and this animated cartoon tells how he spends
his days. Give the guy a tip.
http://www.oddtodd.com/index2.html
- RIAA Wants You to Pay to Stamp Out Crime:
The Recording Industry Association of America, the clueless
music industry trade group with an attitude, would like your
tax dollars to help them bring penniless file-sharing college
students to justice. The group wants more funds allocated to
create additional squads for a program called Computer Hacking
and Intellectual Property (CHIP), which
is part of the Justice Department's initiative to fight cybercrime.
Currently CHIP is meagerly funded, with only $3 million allocated
to ten teams. Although the RIAA applauded the creation of CHIP,
it said it is concerned that CHIP's main focus will be on computer
hacking and not on intellectual property.
The RIAA requested in its testimony that these CHIP units make
intellectual property a top priority. (No word on whether Ponch and Jon will be asked to join.)
The RIAA appears to believe that every MP3 should be considered
a copyright infringement. I disagree. I believe current law
allows consumers to make copies for their personal use. Every
MP3 on my computer was ripped from my CD collection. It's hard
to argue that my use of my legally licensed music for my own
enjoyment on my computer is illegal.
Of course, I agree with the RIAA’s main point, that trading
music files is illegal. While I generally don't buy the music
industry's estimates of revenue lost due to file trading, an
interesting article in Rolling Stone sheds some
light on who is actually getting hurt by file trading: It's
the little guys. The article reported that, although recording
industry sales dropped 3 percent last year, independent retailers,
especially those near college campuses, saw sales drops of 11
percent.
Record sales are down 10 percent overall so far this year. This
compares with an overall growth of 18 percent from 1997 to 2000.
Interestingly, during that same (mostly pre-Napster) period,
sales at stores near campuses dropped 13 percent. So we could
surmise that the recent 11 percent drop among independents merely
continues that trend, although it seems apparent that MP3 trading
is having a big effect.
Is the RIAA position – pursue and prosecute copyright abusers
of all sizes using tax money and industry might – a good strategy?
I argue that it is not in a recent TaylorHarkins newsletter
article I wrote. In the
article, I liken the music industry’s strategy to killing the
golden goose. Napster, Morpheus, Kazaa and all the rest of the
music sharing services could yield a wealth of demographic and
user preference information the likes of which we’ve never seen.
The industry is in a position to know more about their customers’
likes and dislikes than any other industry in history.
Nonetheless, we need to recognize that the recording industry
is actually facing losses, unlike the largely theoretical losses
that Microsoft and other software publishers face from piracy.
ZDNet
- UK Proposes Stiff Penalties for Cell Phone Theft:
The UK’s Mobile Phone (Reprogramming) Bill aims to reduce the
epidemic of cell phone theft. Continental Research estimates
1.3 million people, 4 percent of mobile users, had their cell
phone stolen in the past year. The bill’s proposed penalties
include up to five years in jail. Cell phone thieves have apparently
figured out how to reprogram stolen SIM cards (tiny smart cards
that contain user account specifics), giving the phone an entirely
new number. Stolen SIMs go for between £5 and £60 on the black
market.
Silicon.com
-
Flash!
You’re Compromised! Turns out Macromedia’s
Flash software can be exploited to allow miscreants to run
arbitrary code on your PC. Users are encouraged to download
the fix.
Macromedia
-
SETI
Phone Home: After 500 Million analyses,
the SETI@Home project still isn’t sure we’re alone. That’s
how many data analyses the combined power of millions of computers
has done, for free, since May 1999. The project’s 3,695,182
users process 50 gigabytes of data a day.
Silicon.com
-
Outlook
Bug du Jour: If you use Outlook 2000
or 2002 and have configured it to use Microsoft Word as your
email editor, Word can potentially execute a nasty JavaScript
when you reply or forward email. Get the fix.
Microsoft
-
Fighting Spam: Prospective SNS Reader
and Internet Performance Marketing Consultant Mark
J. Welch recently detailed his anti-spam filtering efforts
on the email discussion list I-Strategy. Since he receives
300 spams a day (!), Mark has set up a set of “include” filters
that first filter “probably good” email into folders. Then
the spam-exclusion filters deal with the rest, automatically
deleting about 90 percent of all incoming email, unseen. Below
are some of his techniques.
Any one of these keywords, if included
in the subject line or any other headers, will blackhole the
email (this is not a complete list):
mortgage, interest, rate, sex, adult,
spam, bulk, snoring, viagra, credit, debt, million, genetic,
hello, virgin, bible, merchant, judgment, ADV:, offshore, stealth,
money, insurance, deal, joke, weight, opportunity, guarantee,
medical, cigarette, essence, plunger, germs, webcam, cartridge,
toner, printer, inkjet, success, HGH, hormone, breast, penis,
inches
[I
understand most of these, but “plunger”??!!]
I also have several dozen "phrase"
filters (more month than money, enable your website, have you
considered, changed my life, are you ready, visited your web
site, red hot, cell phone, etc.) to delete some of the most-frequent
recurring spam themes.
I've also added filters to delete
any incoming email from about a dozen of the commercial email
services (including emailsvc.net and 24/7 RealMedia's m0.net).
Of course I blackhole all email showing
a "from" address from any of several "free-email"
domains (hotmail, netscape.net, yahoo.com, etc.).
When I first turn on my computer in
the morning, it takes from 5 to 10 minutes for these filters
to scan the night's incoming email.
And I usually skim through the "junk"
folder before deleting the 250+ messages that are filtered there
each day. On many days, I find and recover one "wanted"
email from the "junk" folder, and I modify my filters
accordingly to prevent future misdirection of that kind of correspondence.
How
much worse can this problem get before email becomes unusable?
You can take measures like Mark has done, but what if you pay
by the message for your email? What happens when spam becomes
this much of a problem for cell phones? One thing larger companies
can do is use a spam filtering service like MessageLabs’ SkyScan
AS. The rest of us will have to just struggle with the problem.
Adventive’s
I-Strategy
Shameless Self-Promotion Dept.: CTOMentor's
white paper, Peer-to-Peer Computing and Business Networks:
More Than Meets the Ear, is now featured on eBizQ's site.
eBizQ is the insider's guide to e-business.

CTOMentor has just released a new wireless white paper, the
first in The Wireless Future series: You Can Take
It With You: Business Applications of Personal Wireless Devices.
This first paper in the series is free; others that will be
available for a nominal fee will include:
- Islands Make the Net: Wireless Networking
and the Evolving Mesh
- Taking Your Business On the Road: The Car
As Wireless Office
- Standards, Standards Everywhere: A Business
Guide to Wireless Standards
- M-Commerce: Are We There Yet?
- Wherever You Go, There You Are: Mobile Location-Based
Wireless Services
- The Wireless Last Mile: Fixed Wireless Broadband
Services
- Beyond Keyboards, Beyond Wires: Voice Activated
Wireless Services
- Information, Entertainment, and Access At
Your Fingertips: Interactive Wireless Information Services
These white papers will be released over the coming months. To
be notified when a new white paper is released, send an email
to
or check www.CTOMentor.com/wireless/.
You also may want to check out the article I wrote on Instant
Messaging in the latest issue of the TaylorHarkins Insights to
Action newsletter.
Return to Mike’s
Take
|
|
Copyright © 2000-2008, StratVantage Consulting, LLC. All rights
reserved.
Please send all comments to  .
.
|
|
|
|
|

Looking to light up your office, your business, or your city?
The WiMAX Guys™ can help you easily provide secure wireless Internet to your customers.
The WiMAX Guys specialize in designing and running wireless networks. We're experienced, we're quick, and we won't cost you an arm and a leg. Give us a call today provide your users a wireless Internet experience tomorrow.
Call
Mike Ellsworth
Head Guy
952-400-0185
www.TheWiMAXGuys.com
|
Alert SNS Reader Hall of Fame
About The Author
Announcing CTOMentor,
a New Service from StratVantage

Can’t Get Enough of ME?
In the unlikely event
that you want more of my opinions, I’ve started a Weblog. It’s the fashionable
thing for pundits to do, and I’m doing it too. A Weblog is a datestamped
collection of somewhat random thoughts and ideas assembled on a Web
page. If you’d like to subject the world to your thoughts, as I do,
you can create your own Weblog. You need to have a Web site that allows
you FTP access, and the free software from www.blogger.com.
This allows you to right click on a Web page and append your pithy thoughts
to your Weblog.
I’ve dubbed my Weblog
entries “Stratlets”, and they are available at www.stratvantage.com/stratlets/.
Let me know what you think.
Also check out the TrendSpot for ranking of
the latest emerging trends.
In Memoriam
Gerald
M. Ellsworth
March
14, 1928 - July 5, 2003
In Memoriam
Jane C. Ellsworth
July
20, 1928 - July 20, 2003
|



 what happened to the main
StratVantage page
what happened to the main
StratVantage page after the Shredder had
its way with it. More graphics-heavy sites give better results,
like the picture to the left. It’s not useful, but it is interesting.
after the Shredder had
its way with it. More graphics-heavy sites give better results,
like the picture to the left. It’s not useful, but it is interesting.
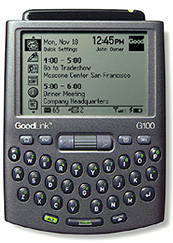 Good is Good Enough:
Good is Good Enough:


