|


Be on the wave or under it™
The News – 08/24/01
The
Ethics of Defense
Alert SNS Reader Andy Stevko raises some very good questions
about a technique some
server administrators use to deal with the Code Red and
Code Red II worms.
First of all, the Code Red worm, in
the news a lot recently, is basically a type of computer virus. Code Red
exploits a security hole in Microsoft’s Internet Information Server, which
is their Web server that runs on Windows NT or 2000 machines. (A variant
also infects Microsoft’s Personal Web Server, which runs on Windows 95, 98,
and ME.) The worm has infected hundreds of thousands of Windows servers,
and even has attacked
DSL routers. If you’ve been experiencing a slowdown in response time on
your Internet connection recently, it could be because of this worm and its
variants.
Code Red uses a technique, called an
exploit, in which it overwhelms a part of the computer’s memory called a
buffer. Once in, it copies a program to an area of the Web site and thus
allows anyone to execute any command on the computer. This is called
installing a backdoor, and this is a bad thing.
Another thing Code Red does is to
flood the local network with traffic, looking for other vulnerable IIS
installations. Once one is found, it repeats its dastardly deed, and so on
and so on. The infected computer becomes a drone, with the aim of recruiting
more drones to use in its ultimate goal of attacking the White House’s Web
servers. Because of the techniques used in this attack, which are similar
to a Denial of Service (DoS) attack, even if a target computer has been
patched to resist the buffer overrun exploit, it still can end up spending
all its time replying to bogus
Web page requests with “Page Not Found” messages. So even if you’ve
been smart, and you’ve protected yourself against Code Red, it can still
affect your computer and your network.
Andy reports that an enterprising
bunch of server administrators have decided to fight fire with fire.
They’ve created a program called a FightBack script that takes advantage of
the backdoor installed on infected computers. According to Andy, “The FightBack
script reads the IP [network] addresses off the request and triggers
another request sent back to the infected server.” This request uses the
backdoor to reboot the infected server, without the knowledge or consent of
that server’s administrator, who probably doesn’t know he or she is
infected. Since the Code Red worm only installs itself in an infected
computer’s memory and not on the hard disk, this clears the infection. But
it doesn’t remove the backdoor.
In essence, the FightBack script
acts as a “good virus.” Andy questions whether there is such a thing:
Worms and Viruses live mainly by exploiting
software cracks to 'own' someone else’s computer. The most evil ones
deliver a nasty payload.
Are there 'good' worms and viruses? A good
virus could contain a neutral payload or perhaps fix/patch the expoit it
used. Would you want one to touch your systems? Nearly every sysadmin says
NO!
But DoS attacks provide little defense. They
leach CPU and soak up bandwidth. It is very hard to even reset a remote
drone.
FightBack servers can be built to control
offending hosts. Is the cure any better than the curse? Would you ever
admit to owning one?
Good questions, and ones that will
be faced more and more often as the antisocial microcephalic
morons who write viruses and worms proliferate. Because many exploits and
viruses can be built using tools requiring little technical knowledge, more
and more bored adolescents are likely to turn from low tech annoyances like
T.P.ing your house or ringing the bell and running away to becoming script
kiddies and a major threat to the Internet. System administrators may
well become more and more desperate and more likely to use questionable
defenses in order to keep their networks and servers operational.
In answer to Andy’s
question regarding the ethics of FightBack scripts: I am uncomfortable with
this approach, but unfortunately, taking the completely ethical approach
could yield a disastrous outcome. Your network could crash. Your servers
could crash. Your business could go out of business. So, yes, fighting back
is an option. However, I think the more ethical way to fight back is to use
a script to try to find the email address of the administrators of the
offending computer. Then, email them and give them some period of time to
rectify the situation. This at least gives them a fighting chance to take
care of the problem themselves. If there is no response, and there might
not be one in the middle of the night or on holidays, for example, do what
you need to do and follow up with an email. And if at all possible, remove
the backdoor. I assume this isn’t done in the Code Red case because it is
not possible.
What do you think? Is it ever
right to make changes on another person’s server? In the absence of other
effective defenses, is a FightBack script ethical? Would you want your
business’ Web server “repaired” without your consent? Send in your
responses, even (especially!) if you’re technologically-challenged, and I’ll
print the most interesting ones in future SNSes.
National
Infrastructure Protection Center
Briefly
Noted
- Shameless Self-Promotion Dept.:
My speech at the Minnesota Entrepreneurs Club pre-meeting workshop on
Tuesday, “Will You Have to Have It? What You Need to Know About
Future Tech and Your Business,” is now available.
Also, my white paper, Taking Control of the B2B Exchange: What's
Next in the Supply Chain Evolution, is now available on Manyworlds and is rated four
stars. I am honored to share the page with eCommerce expert Mohanbir Sawhney.
 Take Two Cameras and Call Me In the Morning: Alert SNS Reader Roger Hamm sends along a pointer
to this innovation that many of us superannuated geezers will
appreciate. Instead of having to swallow a pole for an upper-GI series,
you soon may be able to swallow a wireless camera-in-a-capsule to
check things out. The FDA has given Given Imaging its approval for use
of the camera in upper-GI series. Each pill costs $450, so you’ll want
to be real careful where you go, if you know what I mean. The company
even has cool
videos of the camera in action on its Web site. My first thought
was, it’s pretty dark in there, how can it see? Turns out the camera
has its own light source. The system comprises the camera, a set of
wireless sensors worn around the waist, and a workstation to analyze
the results. Now if they can just develop one for the lower-GI . . . Take Two Cameras and Call Me In the Morning: Alert SNS Reader Roger Hamm sends along a pointer
to this innovation that many of us superannuated geezers will
appreciate. Instead of having to swallow a pole for an upper-GI series,
you soon may be able to swallow a wireless camera-in-a-capsule to
check things out. The FDA has given Given Imaging its approval for use
of the camera in upper-GI series. Each pill costs $450, so you’ll want
to be real careful where you go, if you know what I mean. The company
even has cool
videos of the camera in action on its Web site. My first thought
was, it’s pretty dark in there, how can it see? Turns out the camera
has its own light source. The system comprises the camera, a set of
wireless sensors worn around the waist, and a workstation to analyze
the results. Now if they can just develop one for the lower-GI . . .
Given Imaging
- Passport Correction and Response: Alert SNS Reader Larry Kuhn corrected a couple of
inaccuracies in the previous SNS
regarding Microsoft’s Passport online credentialing system. He points
out that not all cookies are cleartext, a fact I knew but forgot. The
cookie used in the Passport scheme to hold your authentication
credential is binary, and thus not human-readable. Larry agrees that
cookies are easily retrieved from a user’s PC, but points out that “since
the Passport service expires authentication keys on a regular interval
(not sure what that interval is though... ), a stolen cookie is very
soon useless.” This isn’t good enough for me to know that someone can
steal my identity, but only for a little while. One bad transaction
could ruin a person. In addition, Microsoft leaves it up to the Web
site owner to ensure that the authentication cookie is deleted
at sign out: “For security reasons, you must delete all
Passport-related persistent and session cookies from a member's
computer when the member signs out by clicking the sign-out link or by
closing their browser.” Sorry, that makes me nervous.
Larry also takes issue with the assertion that your Windows XP
password and your Passport password will be the same. I have to bow to
his superior knowledge on this one, and note that I didn’t make any of
this stuff up, but got it from noted security expert Avi
Rubin, a researcher at AT&T Labs. Perhaps his information was
dated. It is clear that Microsoft requires
signing up for a Passport to use many of XP’s services.
Larry offers some comments on the whole single sign-on and online
authentication problem:
Larry Kuhn: “This whole issue is a catch
22 for consumers - from a convenience standpoint, I'd really like to only
ever have to identify myself once all day long as I use various
computers... (or better yet, have each computer just recognize me, the way
my friends do when they meet me on the street) - but in order for that to
happen - all these systems need to know me - and if they know me, well -
they know me.”
SNS: "So you're saying,
basically, Passport is cool, you're OK with the level of detail Microsoft
will be privy to, and the single point of failure problems don't bother
you, yes?"
LK: “Yes, I have the same type of
problems with the multiple front door keys for my home that are floating
around among my neighbors and relatives. They know all about my new TV when
they see the delivery truck, they know all about my vacation when I ask
them to let the dog out for a week while I'm gone. It’s a chance I take in exchange for
having some options when I get locked out of the house.
“Also, one other point on "who ya going to
trust?" - I figure MS has a lot more to lose than some no-name guy (or
even the government!) in terms of brand equity if they let my info get stolen
or if they use it for illegal or unsavory purposes. Plus, I might eventually need to sue
someone for damages; it may as well be someone who can pay. So, there's actually some value to me in
enlisting them in protecting my personal data.”
Leaving aside the existential question, “Can we ever truly
know anyone?” Larry points out the fundamental difference between online
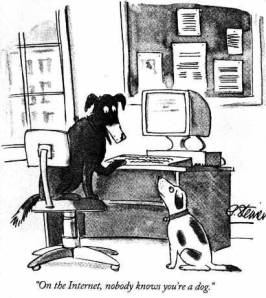
life and offline life: On the Internet, nobody knows you’re a dog. To
establish trust offline, you don’t need to know a person’s Social Security
Number, mother’s maiden name, address, credit card number, and three
references. You meet them, recognize them the next time you meet, work with
them, and build trust.
Online is a completely different story. You don’t necessarily
recognize a person the second time you meet, and you lack a lot of the
information and cues you use to establish trust. Thus, there’s a need for
schemes like Passport, or like biometric methods of determining identity
via fingerprints or iris scans. But there’s something fundamentally more
intrusive about requiring intimate information about my life or my body in
order to identify and trust me. I feel it is much easier to abuse our
relationship if you have this information than it is if we work together or
bank together or worship together in the real world.
As I said last issue, this is obviously a complex issue and
one that businesses need to come to grips with if the Internet is going to
evolve into the kind of marketplace many eCommerce pundits envision.
- New Wireless SIG: Geneer
has created the Midwest Wireless Application Developers Special Interest
Group (SIG) a non-commercial group designed to promote discussion of
wireless developer tips and tools. The first meeting is Tuesday, Sept. 18,
2001, and features Guest Presenter Rod Massie of Motient Corp., provider
of eLinkSM and BlackBerry™ by Motient wireless email services. Rod’s
topic is Developers' Tips & Secrets for Motient's Terrestrial
Network and Motorola's DataTAC Technology. The free meeting runs from 6:00
PM to 8:30 PM at the Marriott Suites, 8535 W. Higgins Road, Chicago,
Illinois.
Can’t Get Enough of ME?
In the unlikely event
that you want more of my opinions, I’ve started a Weblog. It’s the
fashionable thing for pundits to do, and I’m doing it too. A Weblog is a
datestamped collection of somewhat random thoughts and ideas assembled on a
Web page. If you’d like to subject the world to your thoughts, as I do, you
can create your own Weblog. You need to have a Web site that allows you FTP
access, and the free software from www.blogger.com.
This allows you to right click on a Web page and append your pithy thoughts
to your Weblog.
I’ve dubbed my Weblog
entries “Stratlets”, and they are available at www.stratvantage.com/stratlets/.
Let me know what you think. Also check out the TrendSpot for ranking of
the latest emerging trends.
Return
to Mike’s Take
|