|


Be on the wave or under it™
The News – 10/11/01
In
this Issue:
Someone
to Watch Over Us
In the wake of the terrorist
attacks, many people have wondered if one of the new battlefronts will be
cyberspace. In fact, in a previous
SNS, I reported the cracking of a German Islamic extremist Web site and the
posting of subscribers’ names on a Swiss server. How well are we prepared for
infowar? And who will fight it?
One of the forces that will fight to protect US
networks is InfraGard, a cooperative
undertaking between the FBI and an association of businesses, academic
institutions, state and local law enforcement agencies, and other participants.
InfraGard’s mission is to ensure the security of critical US infrastructures
such as energy, banking and finance, water systems, government operations,
emergency services, telecommunications and the Internet. To do so, they work
with the National Infrastructure Protection
Center (NIPC), a governmental organization that is dedicated, in part, to
“detect, deter, assess, warn, respond, and investigate unlawful acts involving
computer and information technologies and unlawful acts, both physical and
cyber, that threaten or target our critical infrastructures.”
The NIPC and the InfraGard are responding to the
requirements of Presidential Decision Directive (PDD) –63, which President
Clinton created on May 22, 1998. The directive orders the strengthening of the
nation's defenses against emerging unconventional threats to the United States
to include those involving terrorist acts, weapons of mass destruction,
assaults on our critical infrastructures, and cyber-based attacks. PDD-63 calls
for a national-level effort to assure the security of the increasingly
vulnerable and interconnected infrastructures of the United States.
While the FBI has called for managers of physical
infrastructure to go to a high alert status, it may be even more important for
networking and computer professionals to be on alert. This is because many
physical infrastructure resources are controlled by computers, and the security
of these computers has been compromised in the past. For example, several times
this past spring, crackers attempted to gain access to the servers at
California's Independent System Operators (Cal-ISO), the agency that manages
the state's electrical supply and decides when rolling blackouts will occur. The
crackers apparently got close to disrupting the flow of power in California
during the rolling blackouts that occurred in May.
Many pieces of critical infrastructure today are
controlled by Supervisory Control And Data Acquisition (SCADA) systems, which
are basically networked computer systems. Like any networked computer system,
SCADA systems can be vulnerable to attacks. Some of these systems, like GE
SmallWorld’s PowerOn™
electrical distribution system or Encorps Virtual Power Plant
power dispatching system, are based on Microsoft Windows products, and many have
Internet-enabled features (using Microsoft’s Internet Information Server (IIS))
for convenience.
Regular readers may remember I am not a fan of
Microsoft products being exposed to the Internet. Well, I’m obviously not
alone. Industry analyst GartnerGroup
agrees:
IIS security vulnerabilities
are not even newsworthy anymore as they are discovered almost weekly . . . As
Gartner warned in 1999, pulling complex application software into operating
system software represents a substantial security risk . . . Microsoft has
discussed its Secure Windows Initiative, which details a well-thought-out
program for improving Microsoft's development processes to avoid repeating the
same security mistakes that led to vulnerabilities in Windows NT and Windows
2000. However, the same old buffer overflow problems appearing in beta Windows
XP code raises doubts over whether the security assurance tools Microsoft has
implemented will effectively reduce the number of well-known security bugs that
continue to show up in Microsoft products. For Microsoft's vision of .NET and
Web services to succeed, Windows XP will have to be significantly more secure
than Windows 2000 has proven to be; otherwise, Microsoft risks losing some
enterprise business to more-secure implementations of Web services.
To reduce their vulnerability, Windows-based SCADA
systems may be hardened and protected by third party software, such as that
available from Visual
Automation. But the fact remains that many critical infrastructure systems
are run by software from a vendor that has, to date, had serious problems with
security vulnerabilities. And that makes me, for one, more than a little
worried. It’s one thing for Web sites to be hacked. Even if the
companies attacked lose millions, it’s only money. It’s yet another thing for
critical infrastructure systems to be attacked, by joyriding script kiddies or
by terrorists; the result could be disastrous. Here’s hoping the newly created Homeland
Security Agency will act to bolster groups like InfraGard and will issue
strong new guidelines for the use and protection of the software that controls
vital services.
In the spirit of acting locally, here are some steps, courtesy
of InfraGard, that you can take to improve your personal and company security:
- Use strong
passwords. Choose passwords
that are difficult or impossible to guess. Give different passwords to all
accounts.
- Make regular
backups of critical data. Backups
must be made at least once each day. Larger organizations should perform a
full backup weekly and incremental backups every day. At least once a
month the backup media should be verified.
- Use virus
protection software. That
means three things: having it on your computer in the first place,
checking daily for new virus signature updates, and then actually scanning
all the files on your computer periodically.
- Use a firewall as
a gatekeeper between your computer and the Internet. Firewalls are usually software products. They
are essential for those who keep their computers online through the
popular DSL and cable modem connections but they are also valuable for
those who still dial in. [Editor’s note: I prefer ZoneAlarm, which is free for personal
use.]
- Do not keep
computers online when not in use. Either shut them off or physically disconnect them from Internet
connection.
- Do not open email
attachments from strangers,
regardless of how enticing the Subject Line or attachment may be. Be
suspicious of any unexpected email attachment from someone you do know
because it may have been sent without that person's knowledge from an
infected machine.
- Regularly download security patches from your
software vendors.
You can also learn more about computer security at the
StratVantage Security
page. If these measures fail, and your company is a victim of a cyber break-in,
it’s important to preserve the evidence so the perpetrators can be located. ZDNet
recommends you take the following steps:
- Record every action
you take. Include the date and time.
- Preserve evidence,
no matter how small.
- Think
prosecution--every action you take should help build a possible court case
against the perpetrators.
- Notify key personnel
immediately.
- Limit the scope of
the attack as quickly as possible.
- Preserve all audits
(disable any system log purges or overwrites).
- Implement additional
security, if necessary or available.
- Review the incident
response plan in light of the recent event and revise accordingly.
Remember that any response plan is just a "work in progress."
You
may be wondering whether you’ll be able to prosecute even if you catch the
criminals. The National Security Institute maintains a list of
computer crime laws by state.
And
hey, hey, hey! Let’s be careful out there!
InfraGard at Iwar.org
Briefly
Noted
- Shameless
Self-Promotion Dept.: I’ve added a new directory to the Directories section of the
StratVantage Web site: Email Newsletters. After conducting a fruitless
search for a central place listing interesting email newsletters, I
decided to establish one myself. I’ve seeded it with newsletters I receive
and find useful. If you’ve got a favorite, send it along and I’ll add it.
StratVantage
Directories
- Advertising Has
Changed: Stan
Hustad, a performance coach with PTM Group, quoted a discussion with advertising
executives John Partilla and Mike Campbell in his recent newsletter. The
pair discussed how advertising will change in the post Tragedy world:
“Cynicism will go by the wayside. It's just not cool anymore.
Relevance will be really important in terms of how you try [to] tie in
what's happened. I see every piece of work that goes out of the
agency, [to see] if it has humor in it, if there is humanity in it, a
humility that feels appropriate. You don't need big focus groups [to
determine what people want]. You can see it in the faces of people
on the street. People are really tender right now. They don't
want to be presented with advertising that is too in-your-face.” Words to
remember if you’re planning an advertising campaign. Stan’s newsletter,
The Coaching Connection, offers tips on self-improvement and performance
optimization as well as business and marketing tips. I heartily recommend
it.
PTM Group
- Toshiba Rolls Out
Handheld: Last week,
Toshiba became the latest vendor to embrace Microsoft’s Personal Digital
Assistant (PDA) Pocket PC platform. Microsoft also announced its latest
revision of the system, dubbed Pocket PC 2002, available now. This is the
first year-named product that Microsoft has released ahead of the year, as
far as I can remember. Toshiba, on the other hand, doesn’t even mention
their new product on their US Web site. Now that’s a great way to roll out
a brand new product! While many industry analysts predict Microsoft will
continue to take share from Palm, the price and still-poor usability
will slow their momentum. The Palm platform got a boost recently when Samsung
rolled out a new color PDA/cell phone for use on Sprint’s cellular
network. The unit uses the Palm operating system, comes with 8MB of memory
and supports Wireless Application Protocol (WAP), HTML and i-mode’s cHTML.
Microsoft
 First US GPRS Network Expands: AT&T, which established
the first General Packet Radio System (GPRS) cellular network in Seattle a
few months ago, is expanding the network to three more cities: Las Vegas,
Phoenix and Portland. Unlike the Seattle area, coverage in these new
cities seems to be fairly extensive. GPRS offers voice and data, with data
speeds as high as 144 Kbps. Typical performance, however, is likely to be
56Kbps, the speed of today’s wireline modems. The company said it’ll roll
out Detroit in the next few weeks, serve about 40 percent of current
customers with GPRS by the end of the year, and serve all its markets by
the end of 2002. First US GPRS Network Expands: AT&T, which established
the first General Packet Radio System (GPRS) cellular network in Seattle a
few months ago, is expanding the network to three more cities: Las Vegas,
Phoenix and Portland. Unlike the Seattle area, coverage in these new
cities seems to be fairly extensive. GPRS offers voice and data, with data
speeds as high as 144 Kbps. Typical performance, however, is likely to be
56Kbps, the speed of today’s wireline modems. The company said it’ll roll
out Detroit in the next few weeks, serve about 40 percent of current
customers with GPRS by the end of the year, and serve all its markets by
the end of 2002.
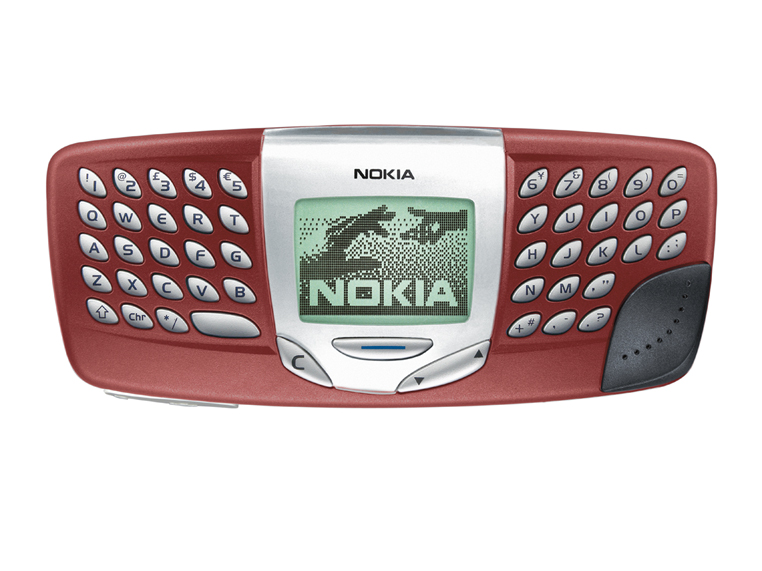
AllNetDevices- Are U Ready 4 a
New Buzzword?
Let’s see. We’ve had eBusiness and e-Tail (stupid buzzword alert),
eCommerce and m-Commerce (mobile commerce). Next, we’ll start hearing
about u-Commerce, or ubiquitous, universal commerce. In the future,
according to Accenture’s
think tank, Accenture Institute for Strategic Change, you can wirelessly
buy anything from anyone anywhere in the world. (Lest we get too
starry-eyed, we need to realize there are places in the world where
livestock is the only going currency.) The company predicts 630 percent growth
worldwide for net-connected wireless devices over the next four years.
Despite its breathlessness, I more or less agree with this forecast. As
I’ve predicted in the TrendSpot, I
fully expect ubiquitous computing, where computing becomes not a place you
go, but a service you get from your environment, to arrive by the end of
the decade. Local area networking schemes like 802.11b (or successors) and
Bluetooth are starting to make this happen today. Will this new acronym
stick? Well, a casual perusal of the Web using Google turns up some
supporters: Visa
(who apparently coined the buzzword), the Association for
Computing Machinery, and South Africa’s McCarthy
Online.
Accenture
- How
Can You Be In Two Places At Once, When You’re Not Anywhere At All? A company called Teleportec has the coolest
technology I’ve seen in a long while. Using three ISDN lines (roughly
384Kbps), a person using their
 $70,000 Teleportec Podium can project his or
her image from the waist up to a remote location and appear lifesized and
in 3D. Only one of the men in the picture to the left is really there; the
other is hundreds of miles away. The company has tried it out with several
businesses. It also makes a large Teleportec Theatre that is 20 feet
across with an 11 foot wide “teleportation zone” designed for panel
discussions or telemeetings. Given the recent events, all kinds of virtual
meeting technology will likely be given a boost (witness WebEx’s 30 percent stock rise on the
first day of trading after the terrorist attacks). If Teleportec’s
technology is as good as they say it is, look for them to put the others
in the shade quicker than you can say, “Help me, Obie-Wan!” The
applications aren’t limited to distance learning and business
conferencing, however, as illustrated by the Digie
award given Teleportec by Realcomm, a realty eCommerce conference. $70,000 Teleportec Podium can project his or
her image from the waist up to a remote location and appear lifesized and
in 3D. Only one of the men in the picture to the left is really there; the
other is hundreds of miles away. The company has tried it out with several
businesses. It also makes a large Teleportec Theatre that is 20 feet
across with an 11 foot wide “teleportation zone” designed for panel
discussions or telemeetings. Given the recent events, all kinds of virtual
meeting technology will likely be given a boost (witness WebEx’s 30 percent stock rise on the
first day of trading after the terrorist attacks). If Teleportec’s
technology is as good as they say it is, look for them to put the others
in the shade quicker than you can say, “Help me, Obie-Wan!” The
applications aren’t limited to distance learning and business
conferencing, however, as illustrated by the Digie
award given Teleportec by Realcomm, a realty eCommerce conference.
Teleportec
- Encryption a Threat? Alert SNS Reader Jeff Ellsworth sends along this article
regarding the role encryption may have played in the recent tragedy. There
is evidence that terrorists have used commonly available Public Key
Encryption techniques as well as the more sophisticated steganography
methods in their communications. Steganography is the embedding of secret
messages in binary files such as image files or music files. The sender
changes a few bits in the file and the result is invisible when viewed or
listened to. There have been claims that the terrorists regularly used
pornography files to communicate. Now Sen. Judd Gregg (R-N.H.) has
proposed making it mandatory that software developers give government
security agents the “keys” to encryption programs when they are created.
The government tried this once before, in 1993 with a technology called
the Clipper Chip. The
idea was everyone would use the government’s encryption scheme, which had
a “law enforcement back door.” This scheme was roundly criticized as
unworkable by pretty much every knowledgeable security expert. Three main
criticisms illustrate the folly of the Clipper Chip:
1) Because the government would keep the Clipper methodology secret, the
security community couldn’t point out any deficiencies
2) Crackers would inevitably find ways to use the back door to their
advantage
3) Nobody in their right minds outside of the US would ever use this
technology if the US government could eavesdrop on them, thus it would be
useless in protecting us from foreign terrorists
I really hope we don’t need to go down the Clipper path yet again. Phil
Zimmermann, the creator of Pretty Good Privacy, a popular encryption
technology, believes human footwork will be more useful in catching
terrorists than more surveillance technologies: “It's not practical to
frisk everyone on the planet to find the one person with a box cutter.”
WashTech.com
- Unsafe
At Any Speed? Alert
SNS Reader Bill Lehnertz sent along a pointer to a McKinsey Quarterly
article, How Fast is Too Fast? It’s a nice analysis of the
“Internet time” mania that gripped many of the dot-coms. The authors
studied 80 Internet companies, including business-to-consumer (B2C)
companies, business-to-business (B2B) companies, and infrastructure
providers. They tried to determine the speed with which each built its
business—and the outcome. One of the companies examined is my favorite
dot-com/exchange success story: Altra Energy.
McKinsey
Quarterly (registration required)
Return
to Mike’s Take
|