Nanotubes May Be For Real
I’ve yammered on before about nanotechnology and the huge disruptive effect commercializing this futuristic-sounding technology will have. I recently put nanotech on the list at the TrendSpot at number 13 after realizing I hadn’t added it before. Many readers may have yawned a bit and thought, “Sounds like Star Wars stuff that we’ll be seeing in about 20 years.”
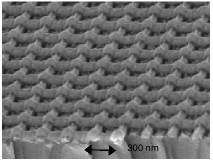 Welcome to the future. If it wasn’t enough of a jolt to realize that 3rdTech is offering the $85,000 Nanomanipulator™ that allows you to manipulate individual molecules and atoms in 3D, or that IBM is makingnanotube transistors in the laboratory, then prepare for the real paradigm shift: Startup Nantero is developing NRAM™, a high-density nonvolatile random access memory chip, using nanotechnology. Specifically, they’re using nanotubes, which are long hollow molecules made up of carbon rings. Nanotubes are 100 times stronger than steel, hard as diamonds, and can conduct electricity as well as copper. Typical Nanotube diameter is approximately 100,000 times smaller than a human hair. (Don’t get me started on the varying estimates of the width of a human hair. In researching it, I found estimates that varied more than a thousandfold. I even found a tidbit that claimed Japanese hair is twice as thick as European hair. So that’s why they appear to be so much better at miniaturization!)The micrograph at right is of a similar memory array developed at MIT. Each square on the grid is 300 nanometers by 400 nanometers.
Welcome to the future. If it wasn’t enough of a jolt to realize that 3rdTech is offering the $85,000 Nanomanipulator™ that allows you to manipulate individual molecules and atoms in 3D, or that IBM is makingnanotube transistors in the laboratory, then prepare for the real paradigm shift: Startup Nantero is developing NRAM™, a high-density nonvolatile random access memory chip, using nanotechnology. Specifically, they’re using nanotubes, which are long hollow molecules made up of carbon rings. Nanotubes are 100 times stronger than steel, hard as diamonds, and can conduct electricity as well as copper. Typical Nanotube diameter is approximately 100,000 times smaller than a human hair. (Don’t get me started on the varying estimates of the width of a human hair. In researching it, I found estimates that varied more than a thousandfold. I even found a tidbit that claimed Japanese hair is twice as thick as European hair. So that’s why they appear to be so much better at miniaturization!)The micrograph at right is of a similar memory array developed at MIT. Each square on the grid is 300 nanometers by 400 nanometers.
Nantero claims to have patented a method of using nanotubes as nonvolatile (meaning the contents don’t disappear when you turn off the power) memory. This could result, according to the company, in “MP3 players with 1000s of songs, PDAs with 10 gigabytes of memory, high-speed network servers and much more.”
The company just received $6 million in venture capital from industry heavyweights like Draper Fisher Jurvetson, and they’re definitely not thinking small, claiming their revenue potential exceeds $100 billion.
If that’s not enough to knock your socks off, you must be wearing nanotube socks, perhaps made in Japan. Gunze Sangyo, Japan’s biggest men’s underwear maker in March unveiled a new process to make fabric using nanotubes. Their rough-edged nanotubes conduct heat more than twice as effectively as copper and would initially find uses in heat sinks to help keep microchips cool. The first device containing the nanotubes is expected to reach the market this year. The tubes are already in production at a joint venture, Nano Graphite Materials Inc, in Ohio.
Argonide Nanomaterials uses a technique that explodes a wire with a huge electrical pulse, firing small particles through cold argon gas. The result is a powder that is 10 to 500 times smaller than that produced by other processes. The company recently received a contract from NASA to investigate the new material for on-board water sterilization filters. Their aluminum nanopowder, Alex®, can be used to accelerate the burning of propellants like those used in artillery shells. Argonide also is developing NanoCeram™, ceramic alumina fibers two nanometers in diameter. The fibers could be used in medical applications as an aid to growing bone because of their bio-adhesive properties. NanoCeram fibers also can be used to remove bacteria and viruses from water.
Nanotubes may also provide a means to set us free from oil dependence. Rhombic is developing a technology that uses carbon nanotubes to store hydrogen in a proton polymer exchange membrane (PPEM) fuel cell. Such fuel cells could replace gasoline as a source of power in cars. Rhombic’s technique grows nanotubes using chemical vapor deposition. Nanotubes turn out to be a great way to store hydrogen, since the space inside the tubes is just wide enough to contain hydrogen molecules. The company hopes to create highly efficient and cheaper fuel cells that combine nanotube hydrogen storage with their innovative Diamond Exchange Membrane (DEM), which separates the anode side from the cathode side in a fuel cell.
Other companies and researchers are trying to create nanomachines, also known as MicroElectroMechanical Systems (MEMS). In fact one MEMS company,Coventor, a provider of MEMS software, ranked 152 on the Inc 500 list of fastest growing companies in the US, experiencing a 1739% increase in sales over five years. I particularly like one of the phrases from Coventor’s Web site: “we work aggressively with customers to summon the future and wire it for power.” O, Future! I summon thee!
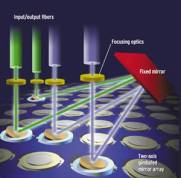 One of the most promising areas for MEMS development is the routing of optical signals in fiberoptic networks. On these networks today, the predominant way to route optical signals is to convert them from light-based to electronic, perform the routing, and convert back to light-based. This obviously introduces delays in delivering the information to its destination. Various companies have tried to create mirror-based systems to eliminate the conversion process, but these systems tend to be slow and bulky. Switches built with nanoscale MEMS-activated mirrors, however, promise to overcome the limitations of current solutions. That’s the approach taken by switch maker OMM. Their MEMS-based optical switches have been carrying live network traffic since early last year. OMM recently announced a 32 X 32 switch which they claim reduces the cost of switching 32 channels by 70 percent.
One of the most promising areas for MEMS development is the routing of optical signals in fiberoptic networks. On these networks today, the predominant way to route optical signals is to convert them from light-based to electronic, perform the routing, and convert back to light-based. This obviously introduces delays in delivering the information to its destination. Various companies have tried to create mirror-based systems to eliminate the conversion process, but these systems tend to be slow and bulky. Switches built with nanoscale MEMS-activated mirrors, however, promise to overcome the limitations of current solutions. That’s the approach taken by switch maker OMM. Their MEMS-based optical switches have been carrying live network traffic since early last year. OMM recently announced a 32 X 32 switch which they claim reduces the cost of switching 32 channels by 70 percent.
 By now you get the idea that nanotechnology is far from science fiction. It’s here, in production, and revolutionizing many industries. I’ve just scratched the surface here, and haven’t even talked about important nanotechnology concepts like self-replication. (For a glimpse of what a future driven by nanotech might look like, I heartily recommend two books: Neal Stephenson’s The Diamond Age, and William Gibson’s Virtual Light.) Companies who make things for a living need to be aware of the challenges posed by new advances in nanotechnology. Even those who make such old tech products as ball bearings need to be aware. The picture at the left represents a concept of ananoscale ball bearing, which might have the capability to accelerate from zero to 500 billion revolutions per second in a fraction of a nanosecond. No one’s building it yet, but just wait.
By now you get the idea that nanotechnology is far from science fiction. It’s here, in production, and revolutionizing many industries. I’ve just scratched the surface here, and haven’t even talked about important nanotechnology concepts like self-replication. (For a glimpse of what a future driven by nanotech might look like, I heartily recommend two books: Neal Stephenson’s The Diamond Age, and William Gibson’s Virtual Light.) Companies who make things for a living need to be aware of the challenges posed by new advances in nanotechnology. Even those who make such old tech products as ball bearings need to be aware. The picture at the left represents a concept of ananoscale ball bearing, which might have the capability to accelerate from zero to 500 billion revolutions per second in a fraction of a nanosecond. No one’s building it yet, but just wait.
O, Future! I summon thee!
Briefly Noted
- Shameless Self-Promotion Dept.: Look for a new directory, debuting early next week: Nanotechnology Resources. Frankly, I was overwhelmed at the amount of information on the Net about this technology and thus didn’t get the directory finished in time for this article. It will feature commercial and academic resources along with pointers to other directories and link pages.
StratVantage Directories - Sprint Readies Visor Phone Plug-in: A GSM cell phone module that plugs into the PalmOS-based Handspring Personal Digital Assistant (PDA) has been available for some time. Now Sprint gets into the act with an add-on module called The Sprint PCS Wireless Web Digital Link. The gadget allows users to make calls and surf the Web on the SprintPCS network and is expected to begin shipping next month for around $250. Right now, however, you can buy it for $49 from Handspring with service activation. Or, you can get the GSM module, with service from Cingular or VoiceStream, for free with activation. OK, I read that news item in Emazing’s Wireless Tip of the Day, and so I go to Sprint’s and Handspring’s sites to check it out. Nothing. Not so much as a word about this module. Either Emazing has a scoop, or this item is erroneous. You decide.
Handspring - Track the Crackers: The DShield site is used by firewall administrators worldwide to post information about attempted break-ins. The site collates the information and displays graphs of the most active cracker network addresses and pie charts of the types of exploits attempted. You can even see a five-day “movie” to see how attempts are changing over time. You can also check out your IP address to see if crackers have used your machine to launch exploits.
DShield - Securing Wireless LANs: As I’ve pointed out in previous issues of SNS, the basic security scheme built in to 802.11b or Wi-Fi wireless networks is easily defeated. So it comes as no surprise that there are folks out there who roam the streets looking for unsecured Wi-Fi connections. What they do with them depends on whether they are white hat or black hat hackers. An article at IBM’s wireless site profiles Internet security consultant Peter Shipley, who trolls the streets of San Francisco in his black Nissan looking for Wi-Fi connections. According to Shipley, “A majority of people are running their APs [Access Points] in effectively open mode – basically wide open, no encryption . . . The only true solution I find at this point – and probably in the future – is to set up IPsec. You wish to place your WAPs or APs – your wireless access points – on a DMZ zone. This DMZ zone should be restricted from the Internet and from your internal network. And the only thing you should allow out of this DMZ zone are connections or computers that have authenticated themselves with IPsec.” What this means in English is: Set up some primary security on your wireless network, based on a standard called IPsec. Don’t trust the built-in security of your Wi-Fi system. Isolate your wireless network from Internet access and from your internal network, and control access to these resources using IPsec.
IBM DeveloperWorks - The High Tech Hunt for Bin Laden: The coalition is using some very high tech gadgets in their hunt for suspected terrorist mastermind Osama Bin Laden, according to a Reuters story. Among the tech are miniature motion sensors hidden on the ground and in rocks that can detect whether caves and bunkers are in use, British Canberra photo-reconnaissance aircraft which can produce images 100 miles from a target, and “keyhole” satellites that can take detailed pictures from space and can be maneuvered into the best orbit to look at Afghanistan.
Security Portal - Coordinated Cyberattacks Stopped on 9/10/01: This item belongs in the Very Strange Coincidence Department. According to California Attorney General Bill Lockyer, well-coordinated cyberattacks that targeted computers in California and 21 countries over three months ended abruptly on September 10th in an eerie prelude to the terror attacks of the 11th. Lockyer said the 120 attacks attempted to strike university, business and government agency computers and were systematic, extensive and appeared to be government sponsored.“There’s a lot of hacking that goes on that’s not this disruptive or expensive,” Lockyer said.“This was notable in that it was sophisticated enough to be beyond the capacity of ordinary hackers. So it suggests that there’s actual government involvement on the other end.”The state is working with the FBI to investigate the attacks.
Contra Costa Times - Java Phones on the Rise: Most of your garden-variety pundits and prognosticators won’t tell you when they’ve been wrong. This is unfortunate, because predicting the future is a very risky business, and because of that, much of what you predict turns out to be wrong. Well, I had two predictions go sour so far this year. I predicted that Japan’s DoCoMo wouldn’t meet their October target for releasing their third generation wireless network. They did. I also predicted that we wouldn’t be seeing Java support on phones for a while. There’s more than 25 Java phones listed on the JavaMobiles site. Hey, if punditry wasn’t hard, everyone would do it!
JavaMobiles - No Comment: Microsoft includes the following statement in the license for FrontPage 2002: “You may not use the Software in connection with any site that disparages Microsoft, MSN, MSNBC, Expedia, or their products or services.” InfoWorld
- Carbon-Based Computer Memory: In one of those wonderful examples of scientific serendipity, a researcher who was hunting for high-temperature superconductors instead found the first non-metallic magnet to work at room temperature. The material is transparent, flexible, made from buckyballs, an exotic form of carbon in which the atoms form a sphere. Since carbon is much lighter than other magnetic materials, the substance could be ideal for creating computer memories of unprecedented capabilities.
New Scientist
Return to Mike’s Take





